Managing Default Access Policies
Default Access Policies are the security policies that are applied by default to the artifacts that are stored in a particular registry. A registry is a system-level graph that stores metadata about artifacts of the same type. For example, metadata about all of your Data Source artifacts is stored in a Data Sources Registry, and metadata about all of your data Model artifacts is stored in an Ontology Registry. A Default Access Policy defines the base permissions to assign to a type of artifact when it is created—before permission inheritance and user-configured sharing is applied.
Any Permission Inheritance that is applied by Anzo and artifact-level Sharing that is configured by users is applied to artifacts in addition to the permissions supplied by the Default Access Policy. For more information about permission inheritance and artifact sharing, see Artifact Access Control Concepts.
This topic provides information about the permission sets that can be assigned to users and groups and describes the default access policies for each registry. This topic also includes instructions for changing access policies.
- Default Access Policy Permissions Reference
- Default Access Policy Reference
- Configuring Default Access Policies
Default Access Policy Permissions Reference
Default access policies use the same predefined permission sets and mechanism for assigning permissions as other artifacts in the Anzo application (see Sharing Access to Artifacts for more information).
There are three predefined permission sets that include a combination of six permissions that can be assigned to the creator of an artifact and other users and groups.
The table below lists the predefined permission sets and describes the privileges that are granted for each permission that is part of the predefined set:
Default Access Policy Reference
There is a configurable Default Access Policy for several of the Anzo registries. To see and manage the Default Access Policies, go to the Administration application, expand the User Management menu, and click Default Access Policies.
Never modify any of the Anzo registries. Changing or removing a registry can irreparably damage your Anzo server.
The sections below provide details about each of the registries for which you can configure default access policies:
- Data Sources Registry
- Global Linked Data Config
- LinkedDataSets Collection Catalog
- Elastic Search Configuration Registry
- Ontology Registry
- Role Registry
- Graphmarts Registry
- Datasets Registry
- Favorites Registry
- Comments Registry
- Linked Data Set Registry
- Persisted Queries Registry
Data Sources Registry
The Data Sources Registry is the system graph that stores metadata about all of the Anzo Data Store, Data Source, and Schema artifacts that have been created in Anzo. Since Data Sources and Schemas have a fundamental relationship in that Schemas are imported from Data Sources, one registry stores metadata about both types of artifacts. The Data Sources Registry access policy is applied by default when a user creates a Data Source or an Anzo Data Store.
In a typical onboarding scenario, a user creates a Data Source and then uses the Ingest workflow to generate the Model, Mapping, and Pipeline artifacts that are needed to ingest the source data and create a graph data set in the Dataset catalog. Since the artifacts created from the Ingest workflow inherit their permissions from the Data Source, the Data Sources Registry policy gets passed to the generated artifacts.
Default Permissions Configuration
The Creator of a Data Source is assigned the Admin permission set for that Data Source and the associated Schemas. In addition, the Creator of an Anzo Data Store is also assigned the Admin permission set for that data store.
The Everyone role is assigned the View permission set for a new Data Source and its Schemas. The Everyone role is also assigned the View permission set for any Anzo Data Stores.
Global Linked Data Config
The Global Linked Data Config Registry is a global policy that applies to all artifacts created in Anzo—unless another Default Access Policy (such as the Data Sources Registry, Graphmarts Registry, or Ontology Registry) applies.
If a user created a Model outside of the Ingest workflow and the Ontology Registry Default Access Policy was removed or unset, the Global Linked Data Config access policy would be applied to that Model artifact.
Default Permissions Configuration
The Creator of an artifact that follows this policy is assigned the Modify permission set for that artifact.
LinkedDataSets Collection Catalog
The LinkedDataSets Collection Catalog Registry is a legacy registry that stores metadata about Linked Dataset Collection artifacts. Linked Dataset Collections were the precursor to Graphmarts and have been deprecated in most organizations. If you do use Linked Dataset Collections, this access policy is applied by default when a new collection is created.
Default Permissions Configuration
The Creator of a Linked Dataset Collection is assigned the Admin permission set for that collection.
The Everyone role is assigned the View permission set for that Linked Dataset Collection.
Elastic Search Configuration Registry
The Elastic Search Configuration Registry is the system graph that stores metadata about all of the Elasticsearch connection artifacts in Anzo. This access policy is applied by default when an Elasticsearch connection is created.
Default Permissions Configuration
The Creator of an Elasticsearch connection is assigned the Admin permission set for that artifact.
The Everyone role is assigned the View permission set for that Elasticsearch connection artifact.
Ontology Registry
The Ontology Registry is the system graph that stores metadata about all of the Model artifacts in Anzo. This access policy is applied by default if a Model is imported or manually created by a user. When a Model is generated from the Ingest workflow, however, the Model inherits the permissions from the related Data Source.
Default Permissions Configuration
The Creator of a Model is assigned the Admin permission set for that Model artifact.
The Everyone role is assigned the View permission set for that Model.
Role Registry
The Role Registry is not used. Roles are not treated like other artifacts in Anzo. Unlike a Data Source, Model, or Graphmart artifact, for example, the permissions for a single Role or subset of Roles cannot be configured separately. Access to create and edit Roles is controlled by the Manage Users, Groups, and Roles permission. For more information, see Role Permissions and Registries.
Graphmarts Registry
The Graphmarts Registry is a system graph that stores metadata about all of the Graphmart artifacts in Anzo. Unlike the artifacts that are generated by the Ingest workflow, which inherit their permissions from the Data Source, all Graphmarts inherit permissions from the Graphmarts Registry Default Access Policy. In addition, Graphmarts contain Data Layers and Steps that describe and group the transformations that take place as the knowledge graph is generated. Since Data Layers and Steps are created in the context of a Graphmart, they inherit permissions from the Graphmart by default.
Default Permissions Configuration
The Creator of a Graphmart is assigned the Admin permission set for that Graphmart artifact.
The Everyone role is assigned the View permission set for that Graphmart.
Datasets Registry
The legacy Datasets Registry is a system graph that stores metadata about non-ontology-backed data sets. This registry is not used. There is nothing that can be created in the user interface that affects this registry.
Favorites Registry
The Favorites Registry is a system graph that stores metadata about artifacts that have been tagged as Bookmarks. This access policy applies by default when a user marks an artifact as a Favorite.
Default Permissions Configuration
The user who tags an artifact as a Bookmark is assigned the Admin permission set. Bookmarks are unique to each user. Users see only their own Bookmarks.
Comments Registry
The Comments Registry is a system graph that stores metadata about any Comments that are added to artifacts. This access policy applies by default to new Comments.
Default Permissions Configuration
The Creator of a Comment is assigned the Admin permission set for that comment.
The Everyone role is assigned the View permission set, which means they can see the Comment but not change or remove it.
Linked Data Set Registry
The Linked Data Set Registry is a system graph that stores metadata about all of the Linked Data Sets, notably the File-Based Linked Data Sets (FLDS) that are listed in the Datasets catalog in the Anzo application.
Default Permissions Configuration
When the Ingest workflow is used to onboard data, the resulting FLDS artifact inherits its permissions from the Structured or Unstructured Pipeline that created it. If raw RDF files are imported to the Dataset catalog, the Linked Data Set Registry Default Access policy is applied to the resulting FLDS artifact.
Persisted Queries Registry
The Persisted Queries Registry is a system graph that stores metadata about the Saved Queries in the Query Builder. This access policy is applied by default when a new query is saved.
Default Permissions Configuration
The user who saves a query is assigned the Admin permission set. By default, saved queries are unique to each creator, and other users do not see the creator's queries.
Configuring Default Access Policies
Follow the instructions below to change the default access policy for a registry.
Changing default access control policies does not change permissions on any existing artifacts. The changes affect only new artifacts that are created after the change.
- In the Administration application, expand the User Management menu and click Default Access Policies. The Default Access Policies screen is displayed.
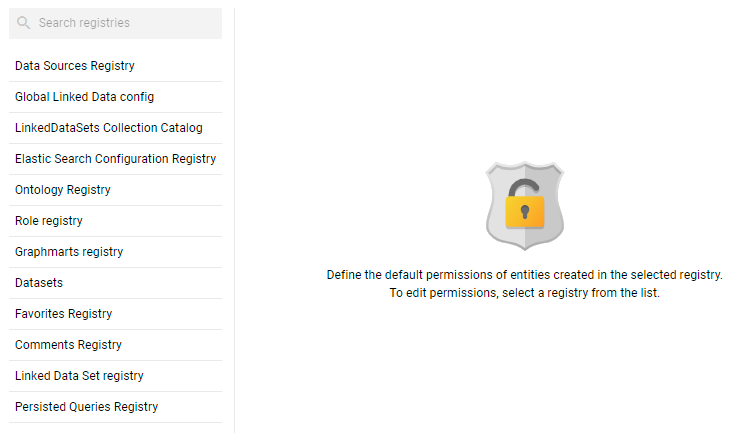
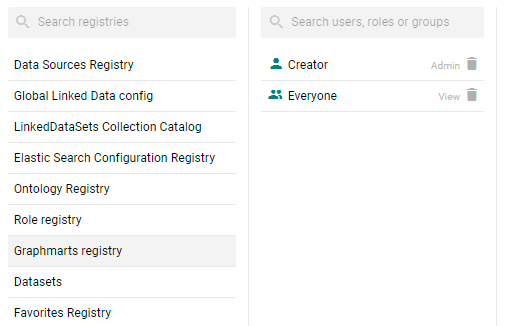
- On the left side of the screen, select the access policy that you want to configure. The current configuration for that policy is shown on the right side of the screen. For example, the image below shows the Graphmarts Registry. The graphmart Creator has Admin permissions, and the Everyone role has View permissions.
- To change a configured user or group, select a name in the list to view the permissions on the right side of the screen. To add a user or group, type a term in the Search field. Then select a name in the result list to view the permissions details. For example, the image below shows the search results for additional groups and selects the Data Modelers group:
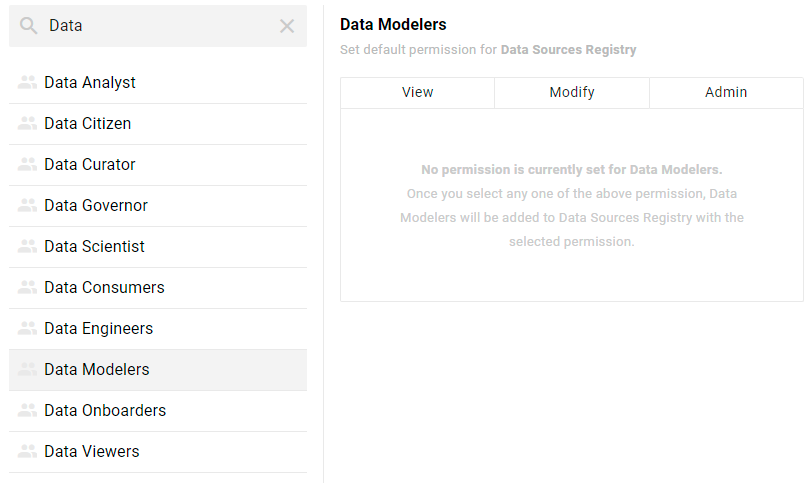
Though Anzo is flexible and allows you to assign default access policies to roles, the recommendation is to control access to artifacts in a registry with users and groups. For more information, see User Management Concepts.
- On the right side of the screen, click the tab for the predefined permission set that you want to assign to the selected user or group. For information about the permission sets, see Default Access Policy Permissions Reference above. For example, the image below assigns the Modify permission set to the Data Modelers group.
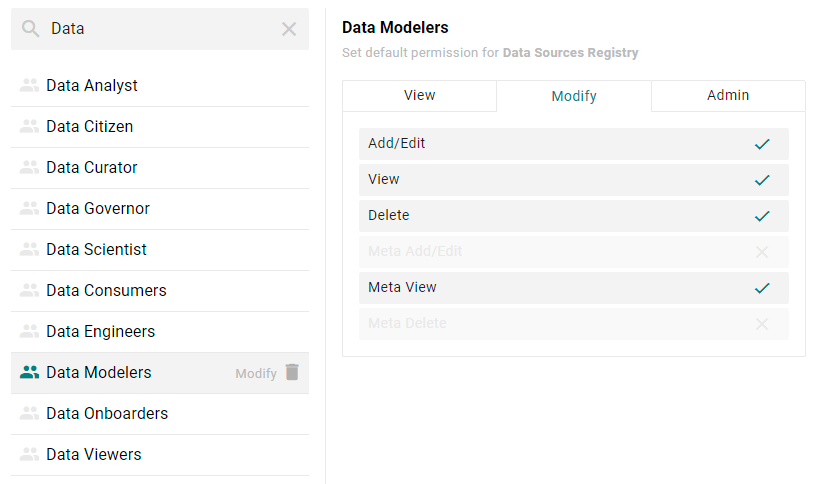
To clear permissions for a user or group, click the trashcan icon (
 ) next to the user, role, or group name.
) next to the user, role, or group name. - To configure additional users or groups, select the name and then repeat the step above to apply a permission set. Changes to access control policies are automatically saved.